Endpoint Security
-
Breaches

54 EDR Killers Use BYOVD to Exploit 35 Signed Vulnerable Drivers and Disable Security
A new analysis of endpoint detection and response (EDR) killers has revealed that 54 of them leverage a technique known…
-
Breaches
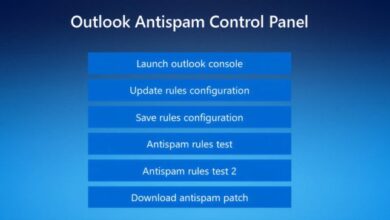
Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
Threat hunters have called attention to a new campaign as part of which bad actors masqueraded as fake IT support…
-
Breaches

Trojanized Gaming Tools Spread Java-Based RAT via Browser and Chat Platforms
Ravie LakshmananFeb 27, 2026Endpoint Security / Windows Security Threat actors are luring unsuspecting users into running trojanized gaming utilities that…
-
Breaches

Hackers Abuse EDRSilencer Tool to Bypass Security and Hide Malicious Activity
Oct 16, 2024Ravie LakshmananEndpoint Security / Malware Threat actors are attempting to abuse the open-source EDRSilencer tool as part of…
-
Breaches

Reynolds Ransomware Embeds BYOVD Driver to Disable EDR Security Tools
Cybersecurity researchers have disclosed details of an emergent ransomware family dubbed Reynolds that comes embedded with a built-in bring your…
-
Breaches

Hackers Abuse EDRSilencer Tool to Bypass Security and Hide Malicious Activity
Oct 16, 2024Ravie LakshmananEndpoint Security / Malware Threat actors are attempting to abuse the open-source EDRSilencer tool as part of…
-
Breaches

Hackers Abuse EDRSilencer Tool to Bypass Security and Hide Malicious Activity
Oct 16, 2024Ravie LakshmananEndpoint Security / Malware Threat actors are attempting to abuse the open-source EDRSilencer tool as part of…
-
Breaches

Winning Against AI-Based Attacks Requires a Combined Defensive Approach
The Hacker NewsJan 26, 2026Endpoint Security / Artificial Intelligence If there’s a constant in cybersecurity, it’s that adversaries are always…

