Researchers Uncover Cicada3301 Ransomware Operations and Its Affiliate Program

Cybersecurity researchers have gleaned additional insights into a nascent ransomware-as-a-service (RaaS) called Cicada3301 after successfully gaining access to the group’s affiliate panel on the dark web.
Singapore-headquartered Group-IB said it contacted the threat actor behind the Cicada3301 persona on the RAMP cybercrime forum via the Tox messaging service after the latter put out an advertisement, calling for new partners into its affiliate program.
“Within the dashboard of the Affiliates’ panel of Cicada3301 ransomware group contained sections such as Dashboard, News, Companies, Chat Companies, Chat Support, Account, an FAQ section, and Log Out,” researchers Nikolay Kichatov and Sharmine Low said in a new analysis published today.
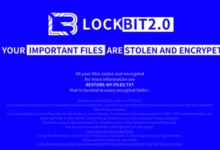
Cicada3301 first came to light in June 2024, with the cybersecurity community uncovering strong source code similarities with the now-defunct BlackCat ransomware group. The RaaS scheme is estimated to have compromised no less than 30 organizations across critical sectors, most of which are located in the U.S. and the U.K.
The Rust-based ransomware is cross-platform, allowing affiliates to target devices running Windows, Linux distributions Ubuntu, Debian, CentOS, Rocky Linux, Scientific Linux, SUSE, Fedora, ESXi, NAS, PowerPC, PowerPC64, and PowerPC64LE.
Like other ransomware strains, attacks involving Cicada3301 have the ability to either fully or partially encrypt files, but not before shutting down virtual machines, inhibiting system recovery, terminating processes and services, and deleting shadow copies. It’s also capable of encrypting network shares for maximum impact.
“Cicada3301 runs an affiliate program recruiting penetration testers (pentesters) and access brokers, offering a 20% commission, and providing a web-based panel with extensive features for affiliates,” the researchers noted.
A summary of the different sections is as follows –
- Dashboard – An overview of the successful or failed logins by the affiliate, and the number of companies attacked
- News – Information about product updates and news of the Cicada3301 ransomware program
- Companies – Provides options to add victims (i.e., company name, ransom amount demanded, discount expiration date etc.) and create Cicada3301 ransomware builds
- Chat Companies – An interface to communicate and negotiate with victims
- Chat Support – An interface for the affiliates to communicate with representatives of the Cicada3301 ransomware group to resolve issues
- Account – A section devoted to affiliate account management and resetting their password
- FAQ – Provides details about rules and guides on creating victims in the “Companies” section, configuring the builder, and steps to execute the ransomware on different operating systems
“The Cicada3301 ransomware group has rapidly established itself as a significant threat in the ransomware landscape, due to its sophisticated operations and advanced tooling,” the researchers said.
“By leveraging ChaCha20 + RSA encryption and offering a customizable affiliate panel, Cicada3301 enables its affiliates to execute highly targeted attacks. Their approach of exfiltrating data before encryption adds an additional layer of pressure on victims, while the ability to halt virtual machines increases the impact of their attacks.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.